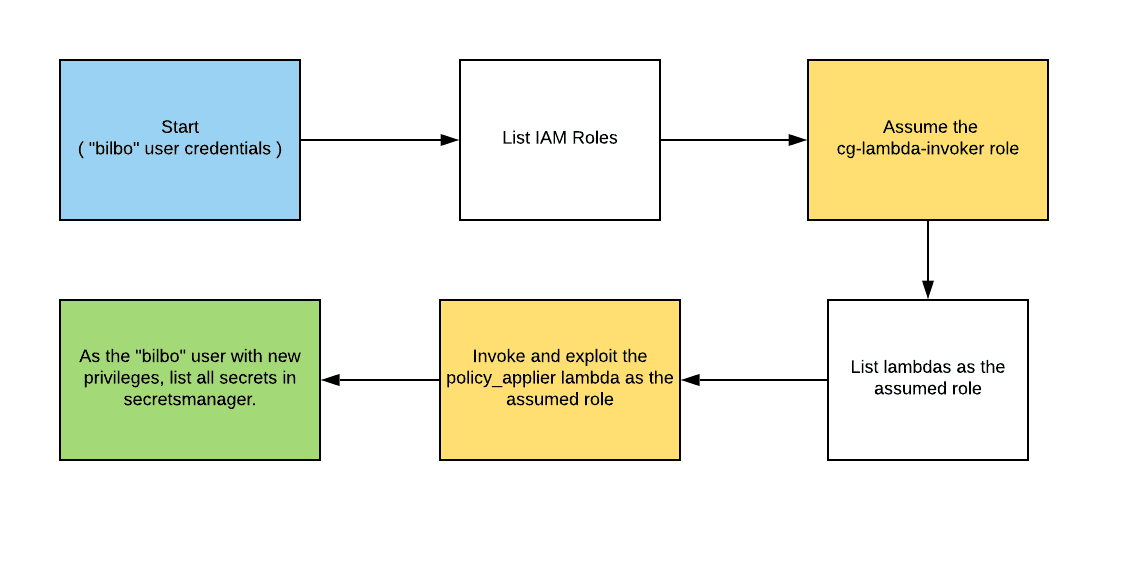
CloudGoat 2.0 - vulnerable_lambda
Breaking Down AWS Attack Paths: A Hands-On Approach To AWS security
Search for a command to run...
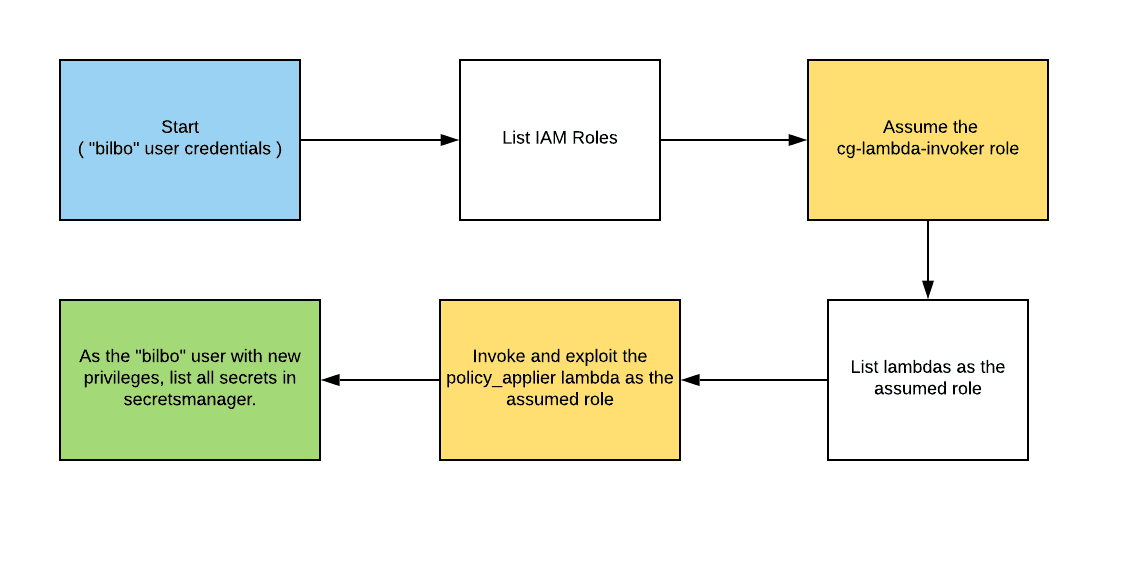
Breaking Down AWS Attack Paths: A Hands-On Approach To AWS security
Streamlining IRSA: New Feature EKS Pod Identity Allows Seamless Authentication
A place where imagination meets innovation for everyone (no coding required)
Learn EKS security with EKS Cluster Games
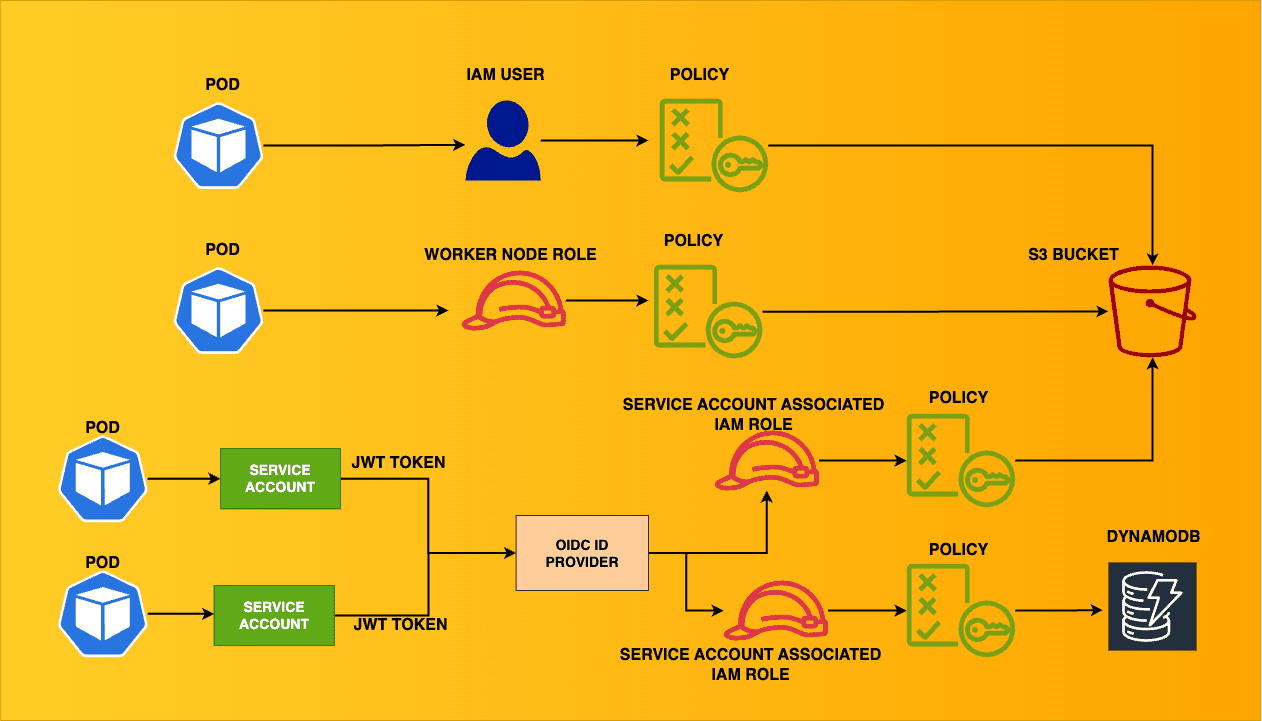
Ensuring least-privilege access in Kubernetes can be complex at times for security & DevOps teams. This blog aims to cover a variety of scenarios where the EKS cluster connects with other AWS resources. This is the architecture of the multiple scenar...
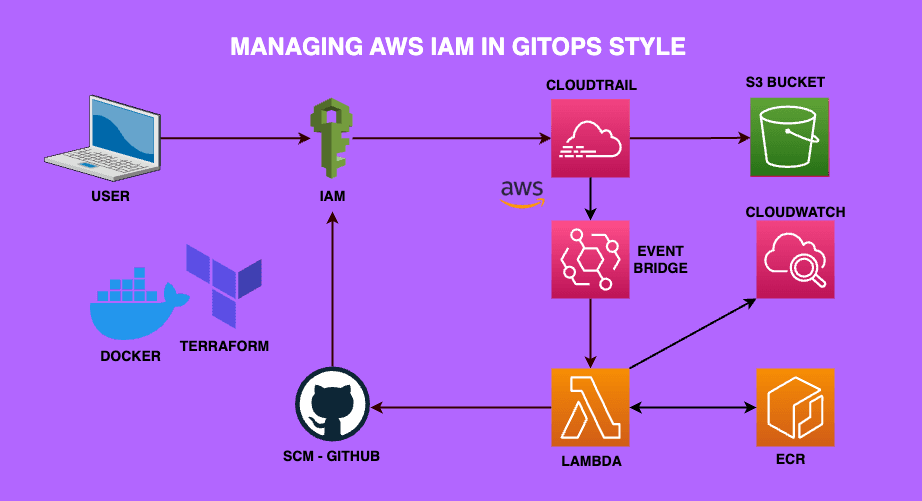
Are you new to AWS & looking for a project to get your hands dirty? This beginner-friendly AWS project focuses on managing AWS IAM using GitOps
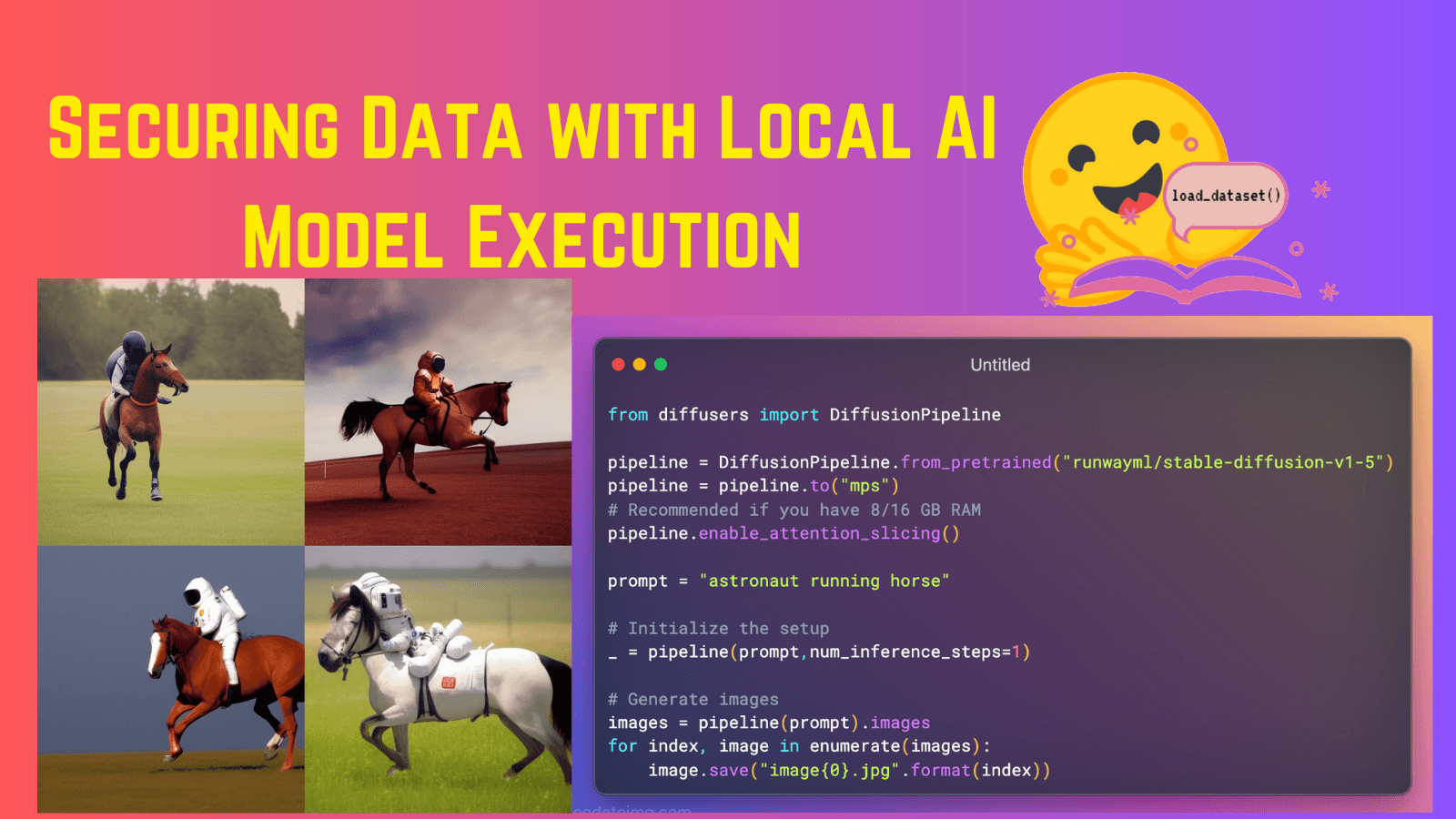
Hugging Face facilitates local AI model execution with pre-trained models, boosting privacy and efficiency while maintaining optimal performance.

Unveiling the Cutting Edge of Cybersecurity at the Premier Conference

Operator require CRDs. In Kubernetes 1.25, CEL validation is in beta! Peek into the process of developing validations for CRDs with & without CEL