Reflections on Black Hat Asia 2023: Learning, Networking, and Inspiration
Unveiling the Cutting Edge of Cybersecurity at the Premier Conference

Rewanth Tammana is a security ninja, open-source contributor, and a full-time freelancer. Previously, Senior Security Architect at Emirates NBD (National Bank of Dubai). He is passionate about DevSecOps, Cloud, and Container Security. He added 17,000+ lines of code to Nmap (famous as Swiss Army knife of network utilities). Holds industry certifications like CKS (Certified Kubernetes Security Specialist), CKA (Certified Kubernetes Administrator), etc.
Rewanth speaks and delivers training at international security conferences worldwide including Black Hat, Defcon, Hack In The Box (Dubai and Amsterdam), CRESTCon UK, PHDays, Nullcon, Bsides, CISO Platform, null chapters and multiple others.
He was recognized as one of the MVP researchers on Bugcrowd (2018) and identified vulnerabilities in several organizations. He also published an IEEE research paper on an offensive attack in Machine Learning and Security. He was also a part of the renowned Google Summer of Code program.
Black Hat Asia 2023, held in the vibrant city of Singapore, surpassed all expectations as it brought together cybersecurity professionals from across the globe. This prestigious event served as a hub for knowledge sharing, networking opportunities, and an abundance of inspiration, leaving attendees empowered and enlightened.
At Black Hat Asia 2023, I had the chance to demonstrate our tool, Damn Vulnerable Bank.

The entire arsenal of presenters!

The conference featured an extensive lineup of captivating sessions that showcased the forefront of cybersecurity advancements. Among the standout presentations, Xiaosheng Tan's keynote address addressed the pressing importance of data security, shedding light on emerging laws and regulations shaping the landscape. Notably, Tan emphasized the significance of Privacy Enhanced Computing (PEC) and its potential impact on the industry.
Another noteworthy session was "Automated Bots as Threat Actors," which delved into the integration of machine learning (ML) and artificial intelligence (AI) in the realm of security. Attendees were captivated by the discussion on leveraging ML and AI to detect patterns, identify attacks, and combat the increasing sophistication of threat actors.
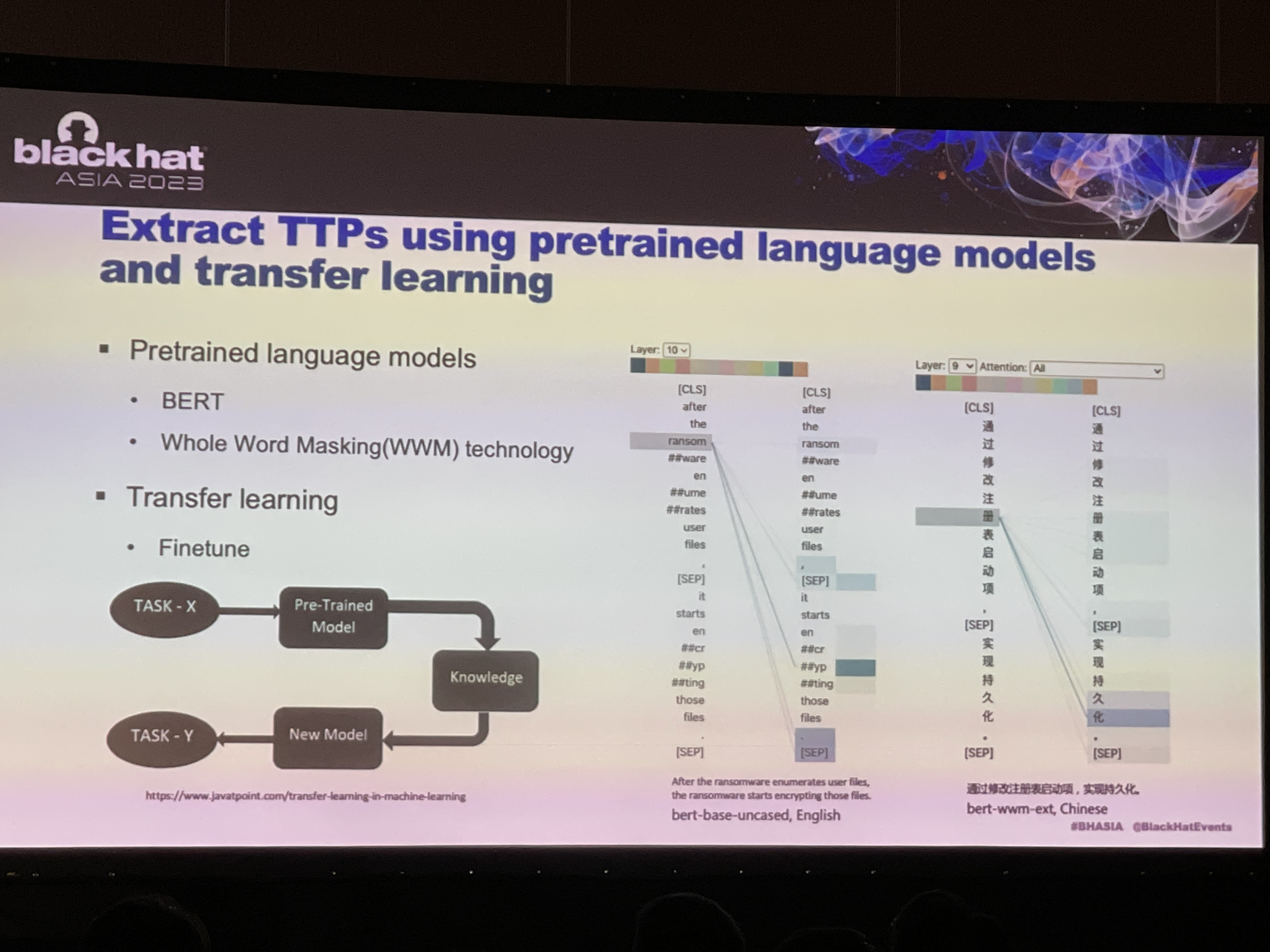
During the event, attention was drawn to the Darknet's "Bots as a Service (BaaS)" offering, revealing the underground economy that fuels cybercrime. The exposure of tools like OpenBullet2 and the exploration of various language models such as GPT-3, GPT-4, LaMDA, BLOOM, XLNet, GPT-Neo, Ernie 3.0 Titan, Minerva, and LLaMA opened new possibilities in areas like credential stuffing attacks and TTP extraction using ML models.
A fascinating topic that garnered significant interest was knowledge graph construction and semantic web-building techniques, which showcased innovative approaches to extract insights and understand the complex relationships between entities in the cyber landscape. The integration of LLM (Large Language Models) in cyber security proved to be a game-changer, unveiling new avenues for threat identification and malware detection.
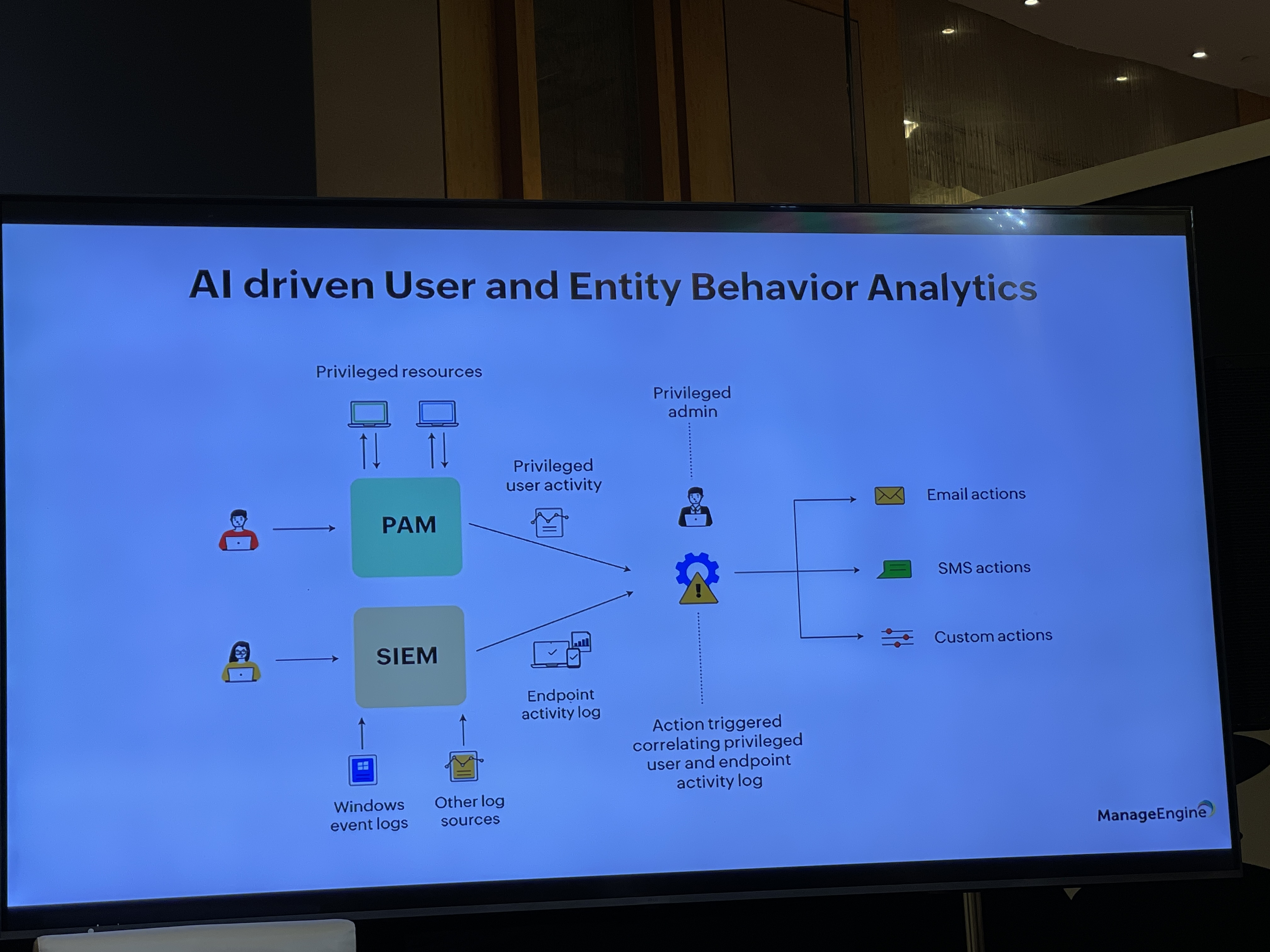
Among the engaging sessions, the discussion on User Entity Behavior Analytics (UEBA) captured attention, showcasing its effectiveness in identifying suspicious behavioral patterns and aiding in detecting shoulder surfing attacks and malware infiltrations.
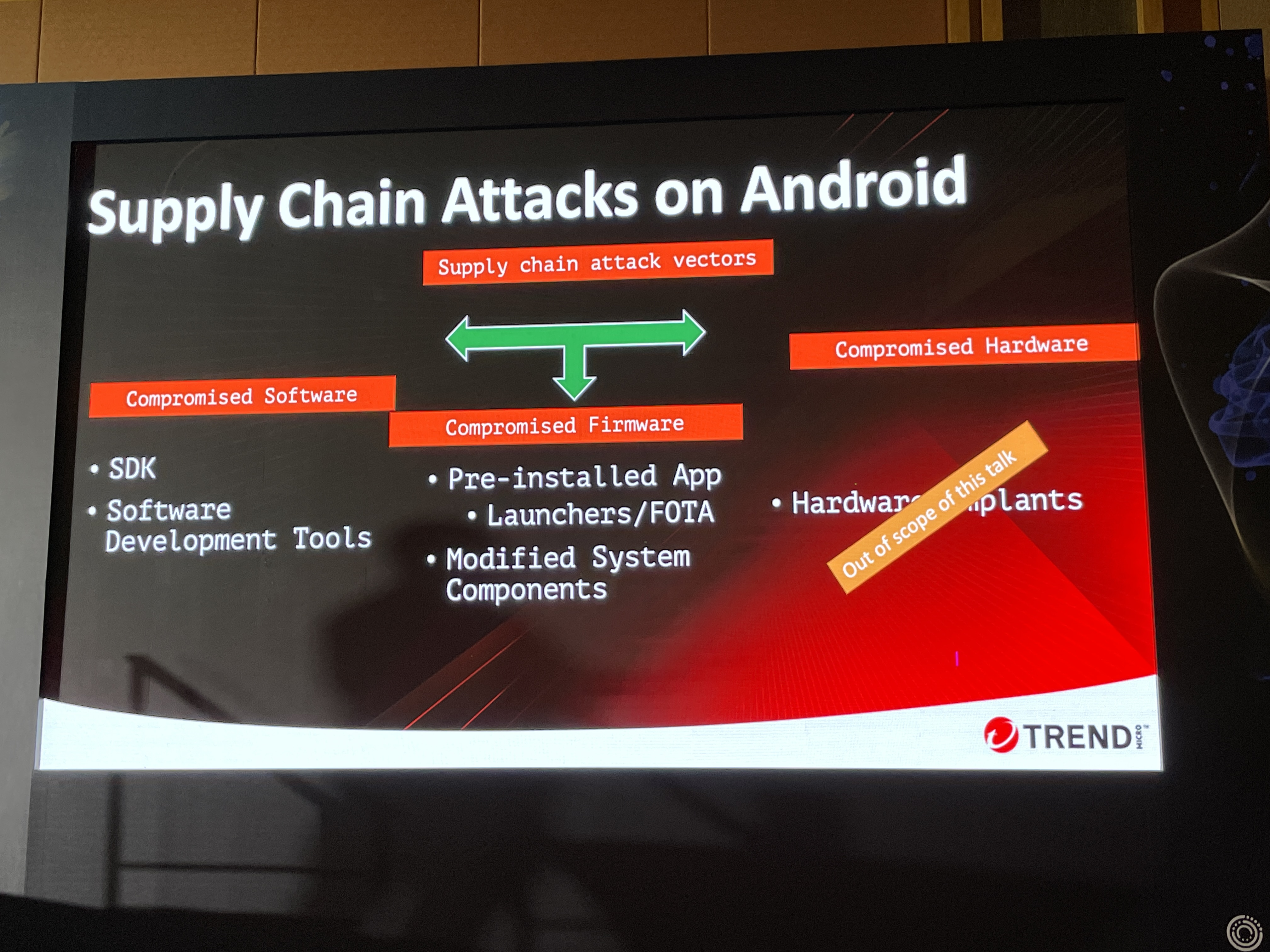
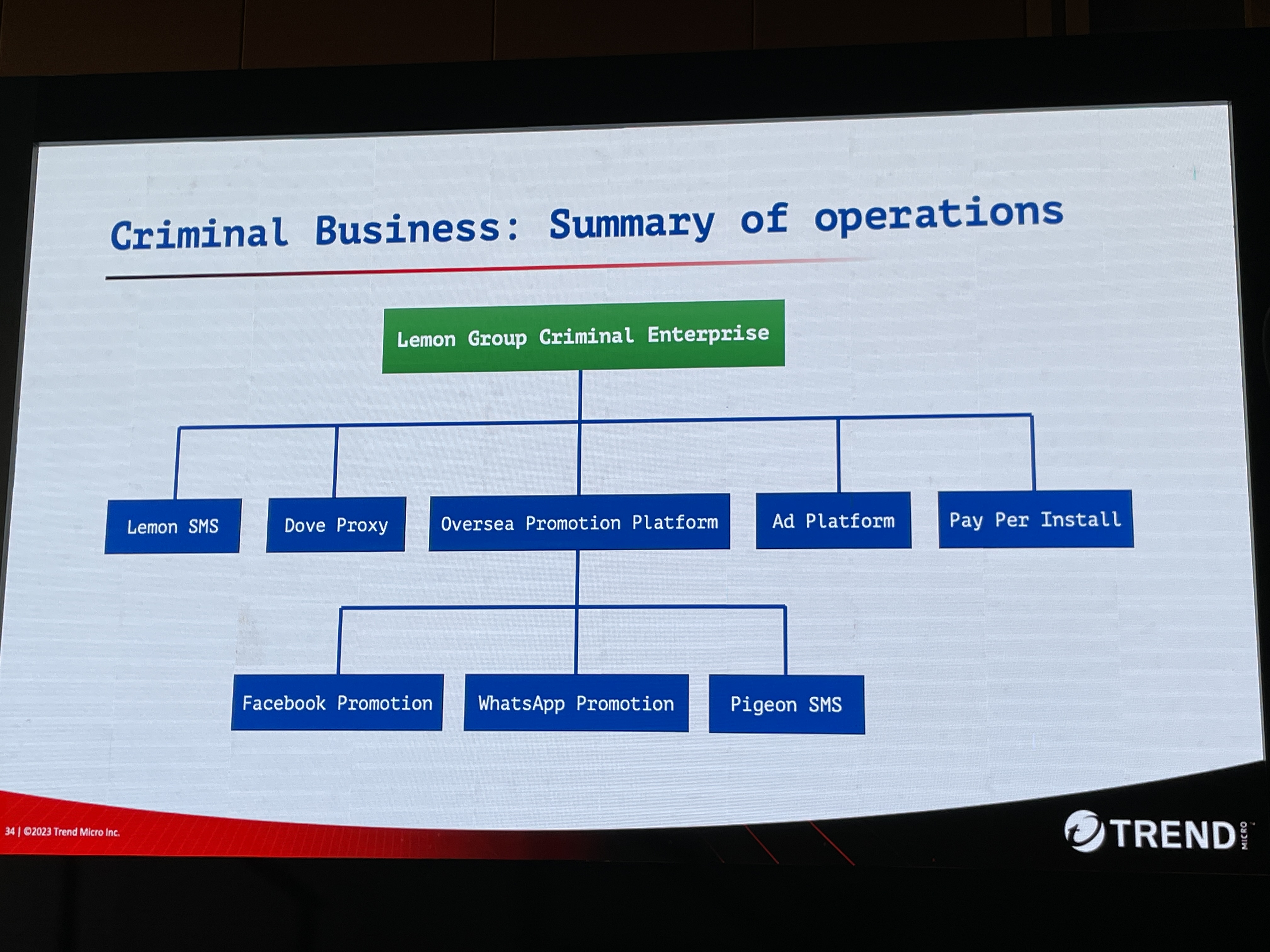
Throughout the conference, attendees were exposed to groundbreaking research and revelations. One particularly enthralling presentation explored the methods employed by criminals to compromise millions of mobile devices. The investigation unveiled intricate implant delivery and management systems, shedding light on the dark underbelly of compromised ROMs and their suspicious DEX files.
ROM compromise trends over the years.
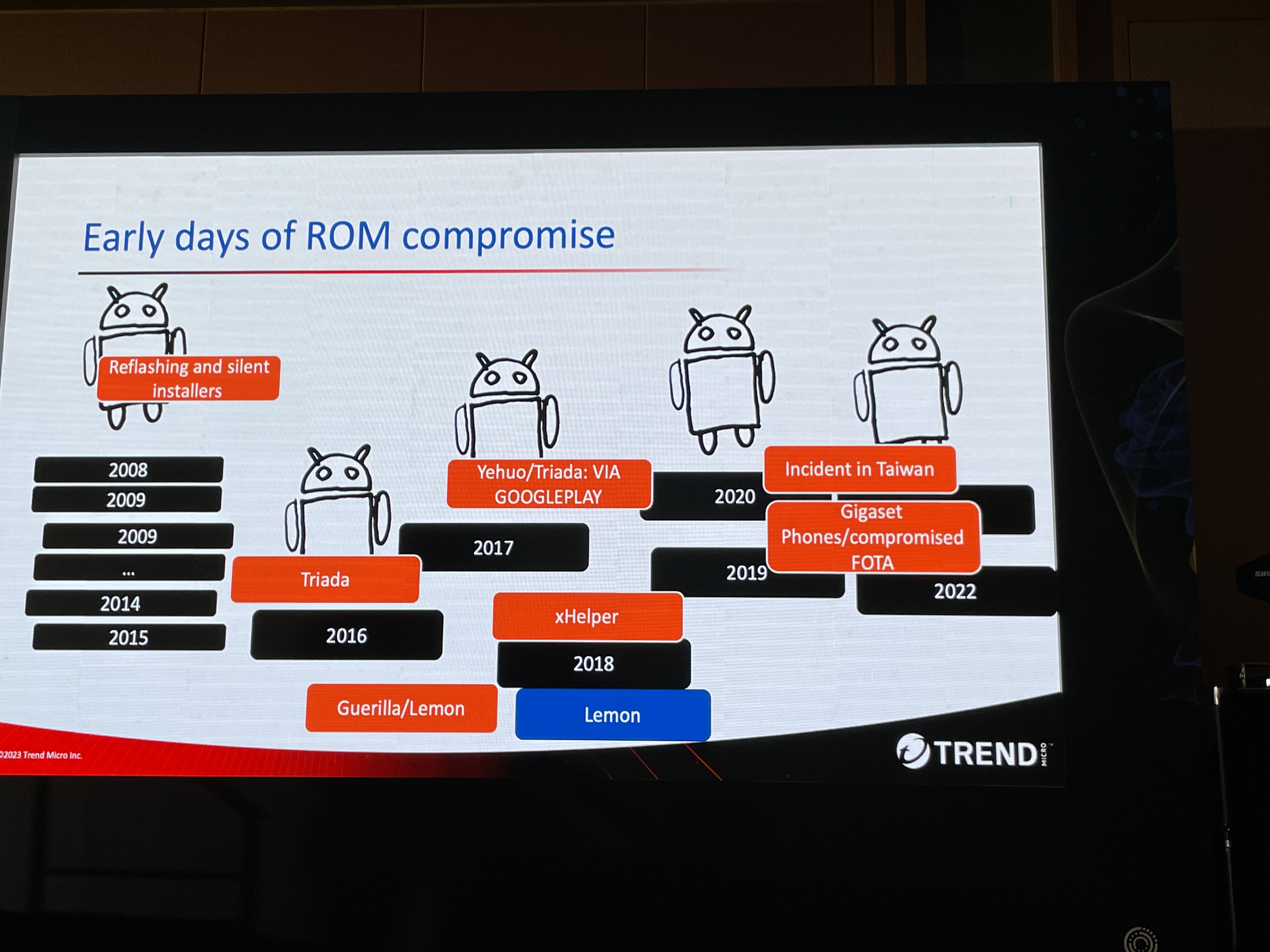
The hackers behind these operations proved to be highly organized, establishing an elaborate network of operations and multiple business entities. Astonishingly, the group boasted the accomplishment of having 8.9 million active devices under their control at one point, displaying their audacious activities on their branded website.
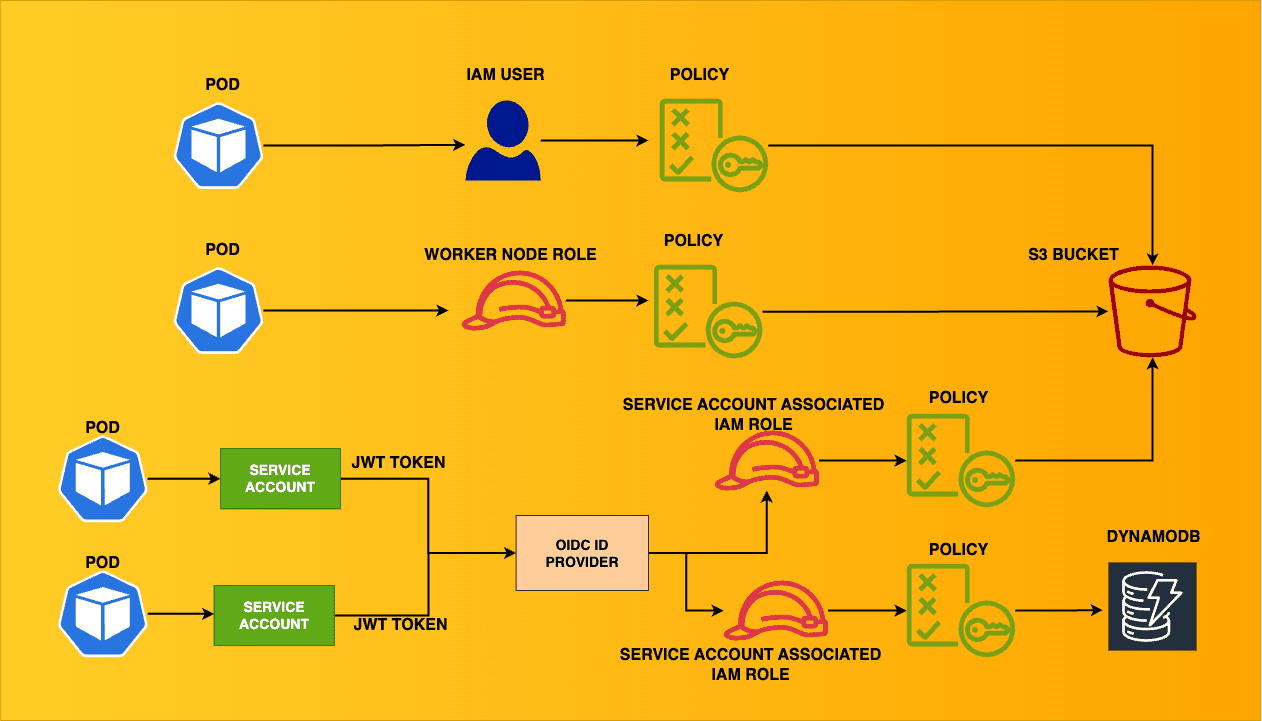
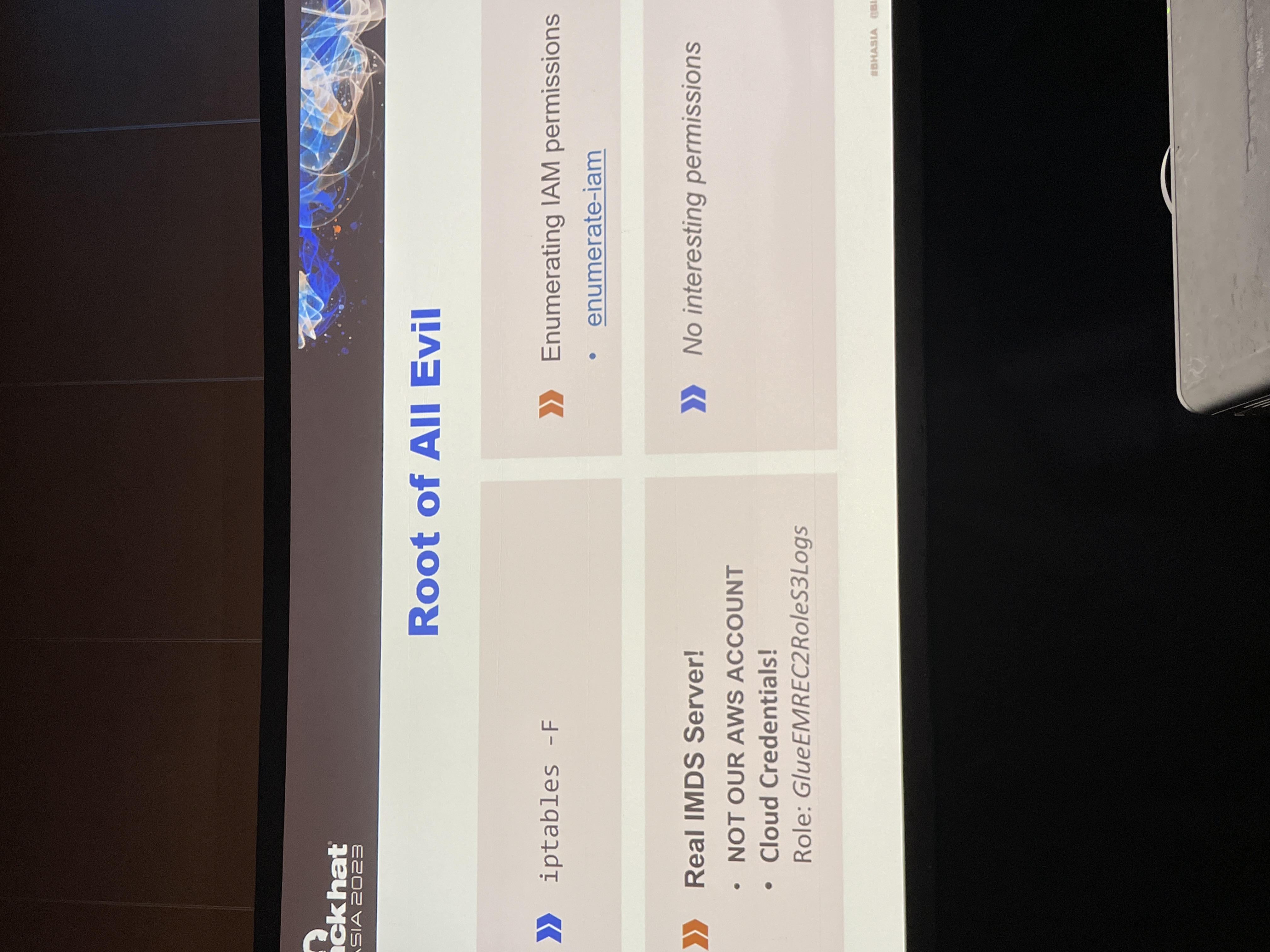
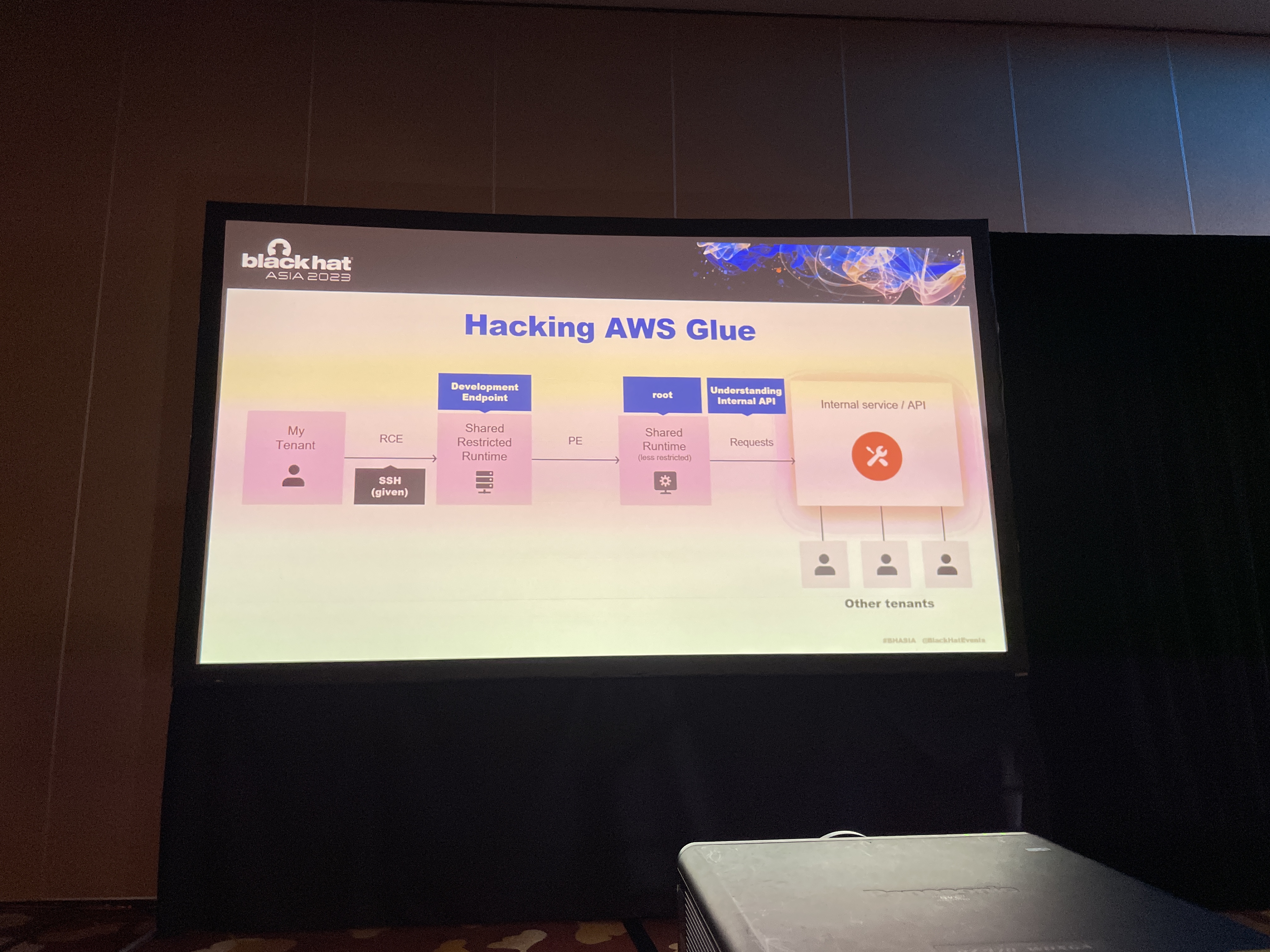
Furthermore, the conference shed light on the exploitation of internal undocumented services within AWS and Azure. The insightful presentation uncovered vulnerabilities in AWS Glue services, revealing jar files that contained information about unexposed services. The session also explored the hacking of managed data services, providing attendees with valuable insights into potential weaknesses in these cloud platforms.
A high-level overview of AWS services Glue hack.
Another captivating talk focused on the exploitation of isolation in WPA3, exposing the vulnerabilities to deauthentication and sleep attacks. The session provided a deeper understanding of the intricacies of wireless security protocols, emphasizing the need for robust defenses against emerging threats.
Showcasing the Arsenal of Innovation
The Black Hat Asia 2023 Arsenal exhibited a diverse range of cutting-edge tools and frameworks that captured the imagination of attendees. Some notable highlights included:
AADInternals: An Azure AD and M365 hacking and administration toolkit.
Purplesharp: An automated adversary simulation tool designed for Windows environments.
uftrace: A dynamic function tracing tool for C/C++/Rust programs.
Osmedeus: An all-in-one reconnaissance framework for building personalized reconnaissance systems.
Bluemap: An interactive tool tailored for Azure exploitation, enabling thorough assessments of Azure environments.
rengine: An automated reconnaissance framework designed to gather information and identify potential vulnerabilities.
squarephish: An advanced phishing tool that combines the OAuth Device code authentication flow with QR codes for highly effective phishing attacks.
Threatseeker: A threat-hunting tool that utilizes Windows event logs for comprehensive analysis and detection.
GodPotato: A tool capable of escalating privileges using the ImpersonatePrivilege permission.
CureIAM: A solution designed to streamline the cleanup of over-permissioned IAM accounts in Google Cloud Platform (GCP) infrastructures.
PoC against flying drone: A proof-of-concept demonstration showcasing an attack against a flying drone.
PyExfil: A Python package that enables data exfiltration from compromised systems.
Faceless: A deepfake detection tool, vital for combating the rise of synthetic media.
Empowering Cybersecurity with Language Models
The conference also underscored the significant role of Language Models (LMs) in the realm of cybersecurity. LMs like GPT-3, GPT-4, LaMDA, BLOOM, XLNet, GPT-Neo, Ernie 3.0 Titan, Minerva, and LLaMA were recognized for their potential in various applications, including credential stuffing attacks and the extraction of Techniques, Tactics, and Procedures (TTPs) using ML models.
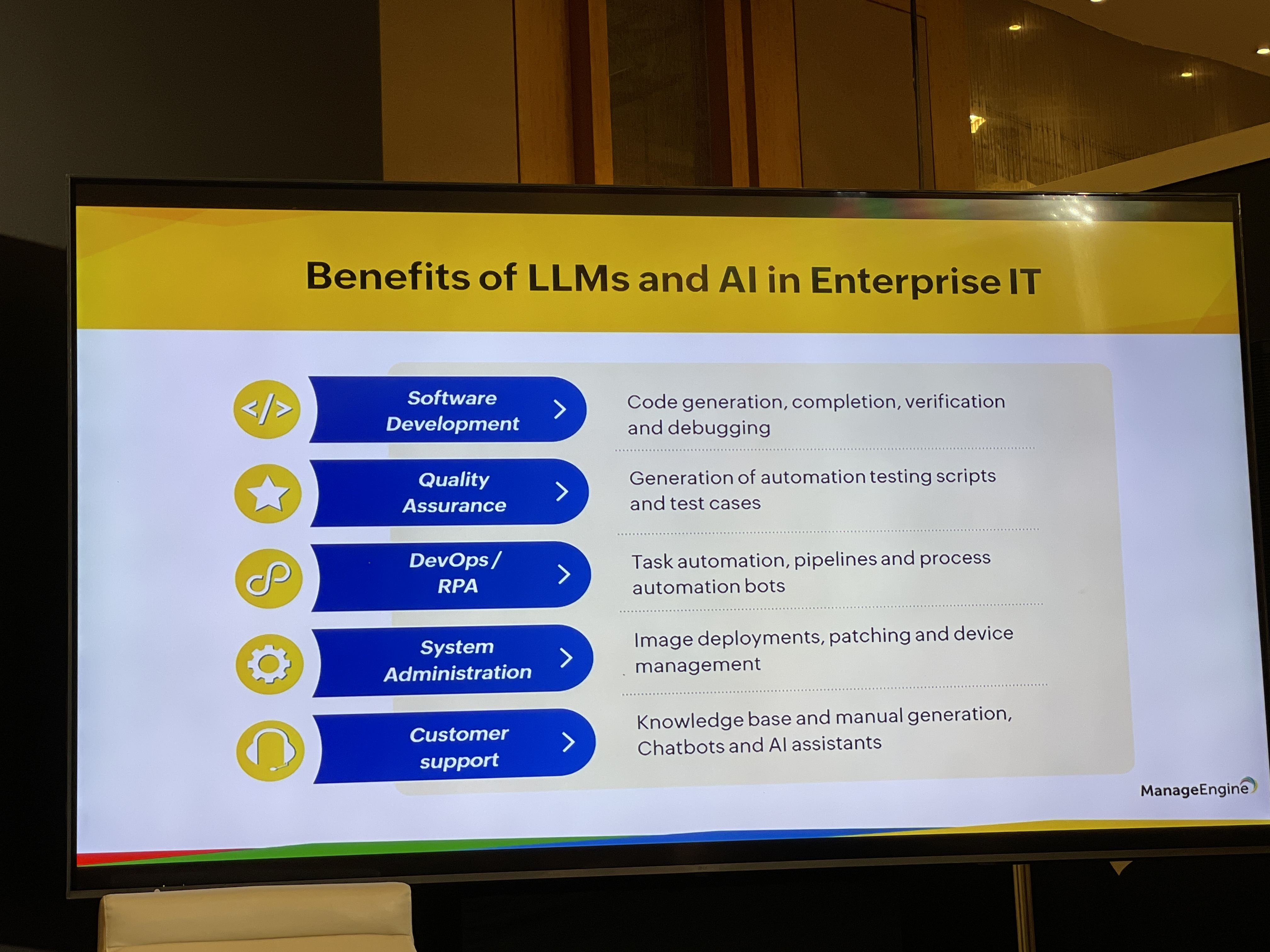
Behavioral analysis using User Entity Behavior Analytics (UEBA) was another area where LMs showcased their effectiveness, enabling the identification of malware attacks and anomalous user behavior. This breakthrough technology offered promising solutions for safeguarding digital ecosystems from evolving threats.
The powerful Network Operations Center (NOC) at Black Hat Asia 2023 demonstrated the vast amount of metrics collected to monitor and analyze network activity. These metrics provided invaluable insights into identifying potential security breaches and ensuring the continuous protection of critical infrastructure.

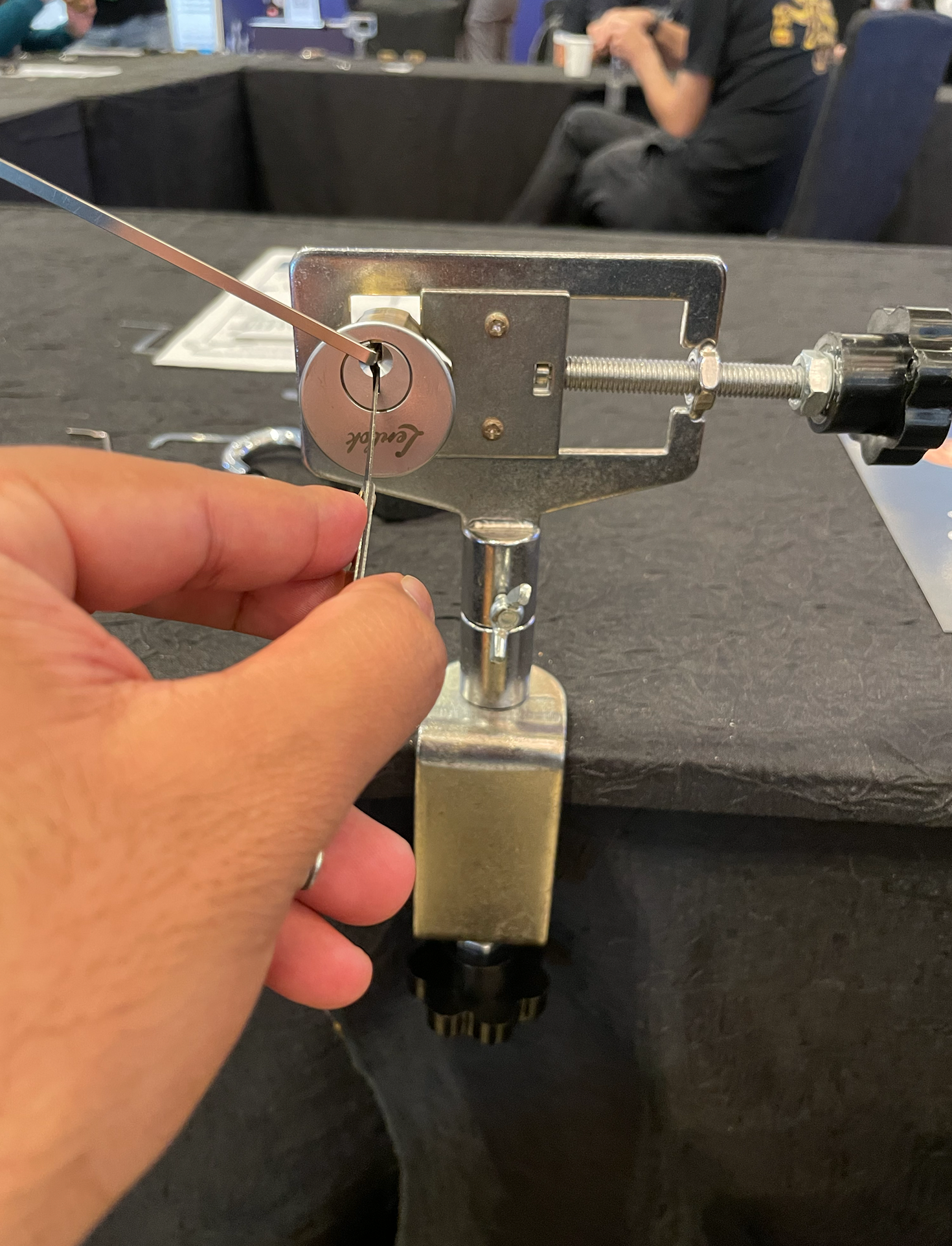
Some hideous hands-on sessions on RFID hacking, lock picking, deep fake detections & lot more. I picked up a few locks 😉
Conclusion
In conclusion, Black Hat Asia 2023 was an exceptional event that brought together cybersecurity professionals from around the globe. Attendees were treated to captivating presentations, enlightening discussions, and access to a diverse range of innovative tools and frameworks.