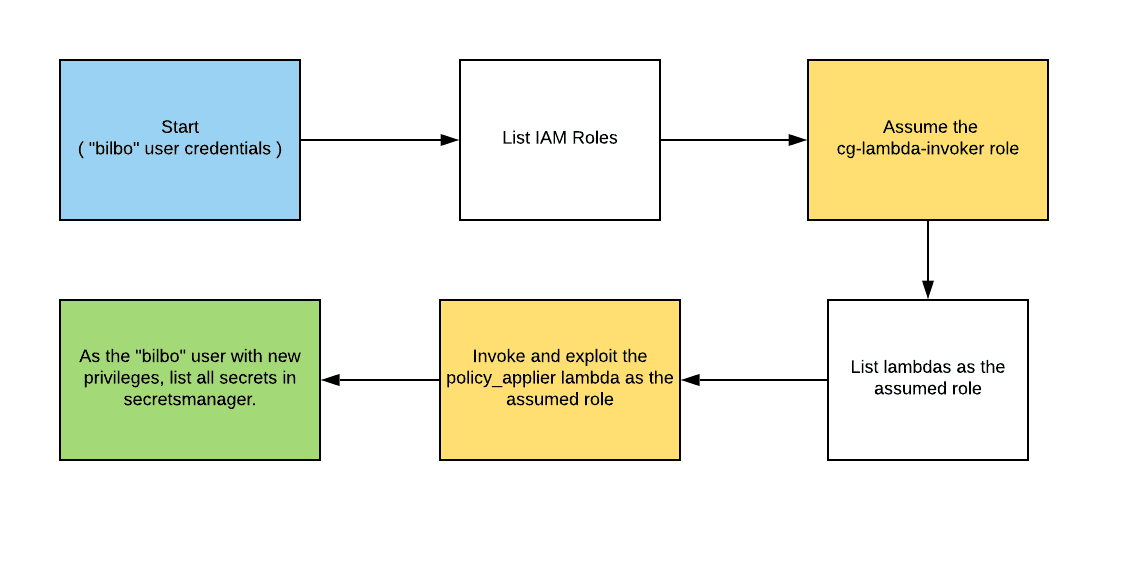
CloudGoat 2.0 - vulnerable_lambda
Breaking Down AWS Attack Paths: A Hands-On Approach To AWS security
Dec 26, 20234 min read387
Search for a command to run...
Articles tagged with #security
Breaking Down AWS Attack Paths: A Hands-On Approach To AWS security
Streamlining IRSA: New Feature EKS Pod Identity Allows Seamless Authentication
Learn EKS security with EKS Cluster Games
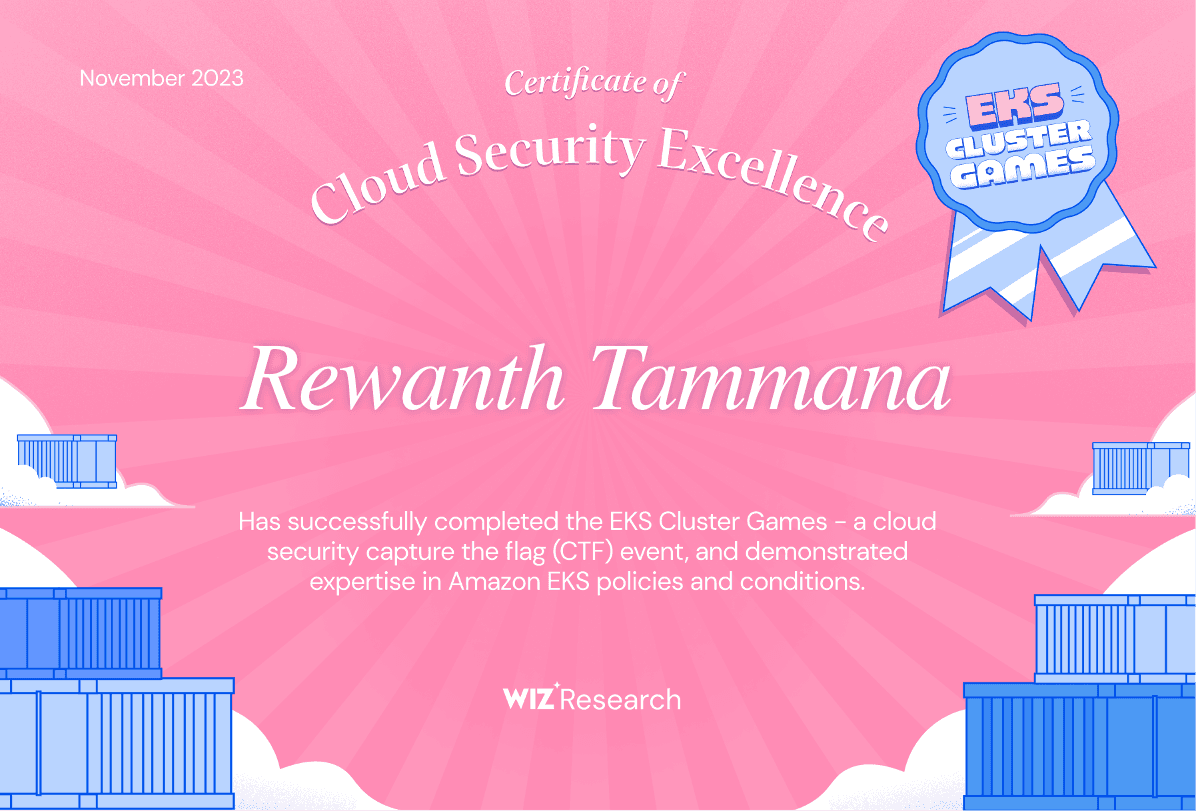
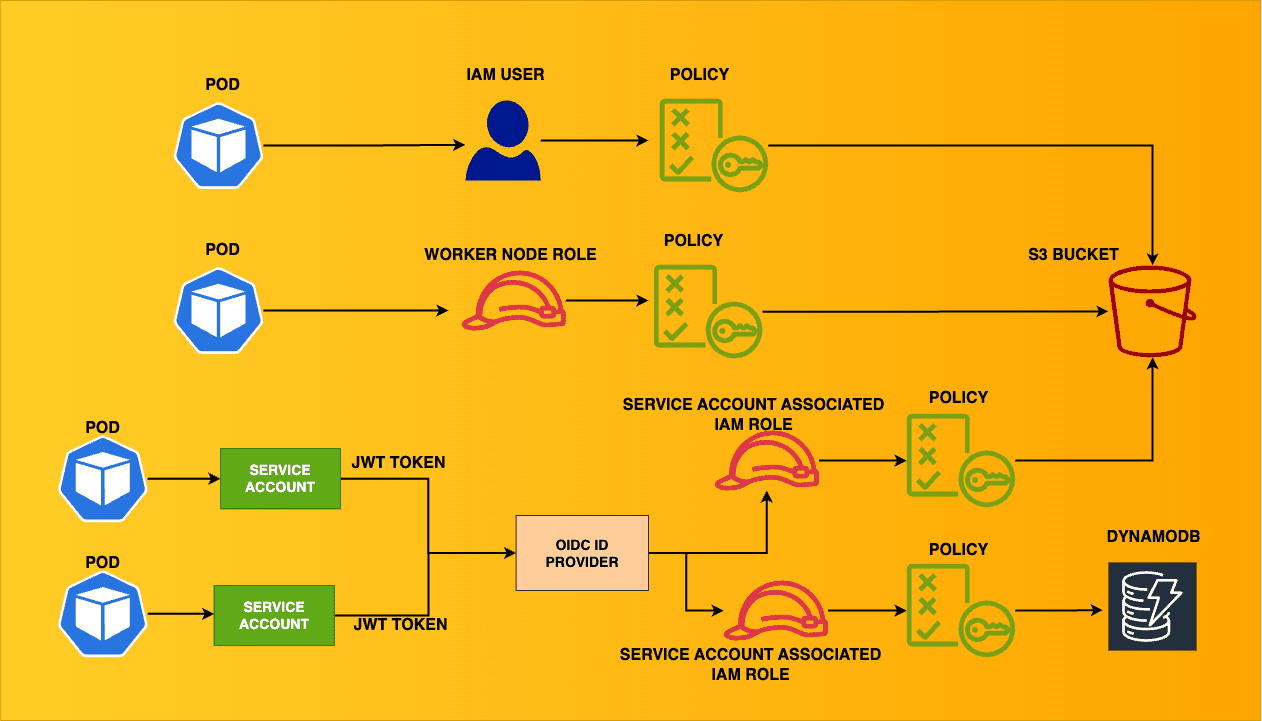
Ensuring least-privilege access in Kubernetes can be complex at times for security & DevOps teams. This blog aims to cover a variety of scenarios where the EKS cluster connects with other AWS resources. This is the architecture of the multiple scenar...
Unveiling the Cutting Edge of Cybersecurity at the Premier Conference

Trivy now supports scanning AWS resources for security misconfigurations
