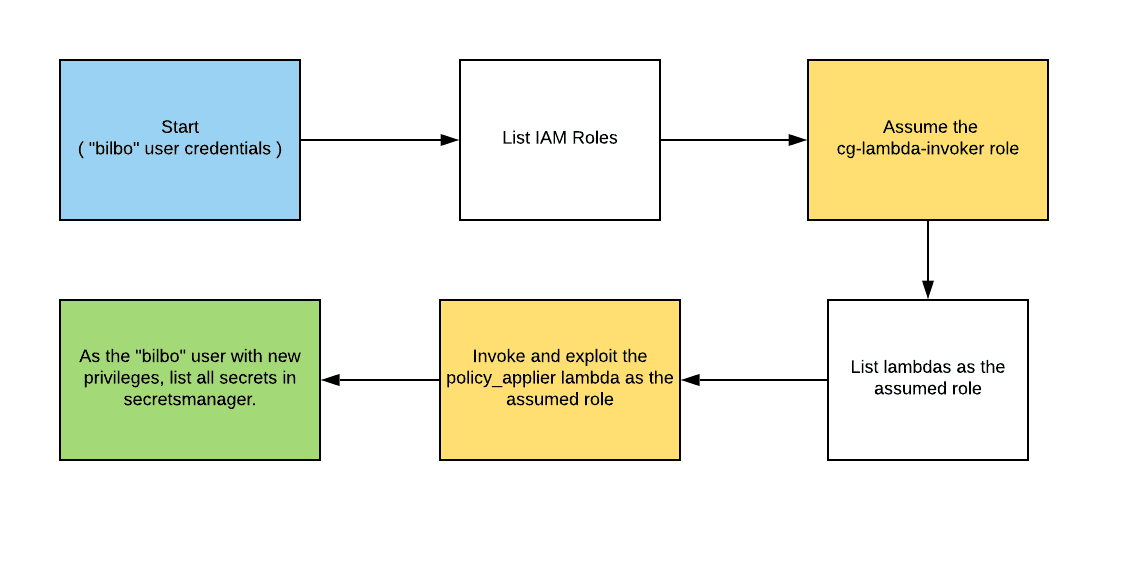
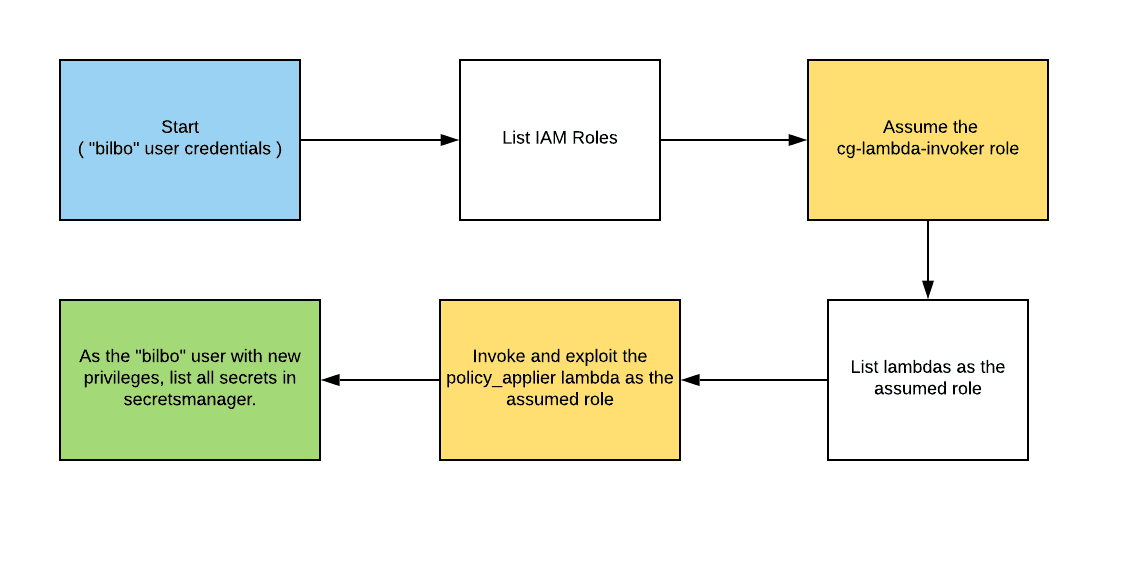
CloudGoat 2.0 - vulnerable_lambda
Breaking Down AWS Attack Paths: A Hands-On Approach To AWS security
Dec 26, 20234 min read395
Search for a command to run...
Articles tagged with #aws
Breaking Down AWS Attack Paths: A Hands-On Approach To AWS security
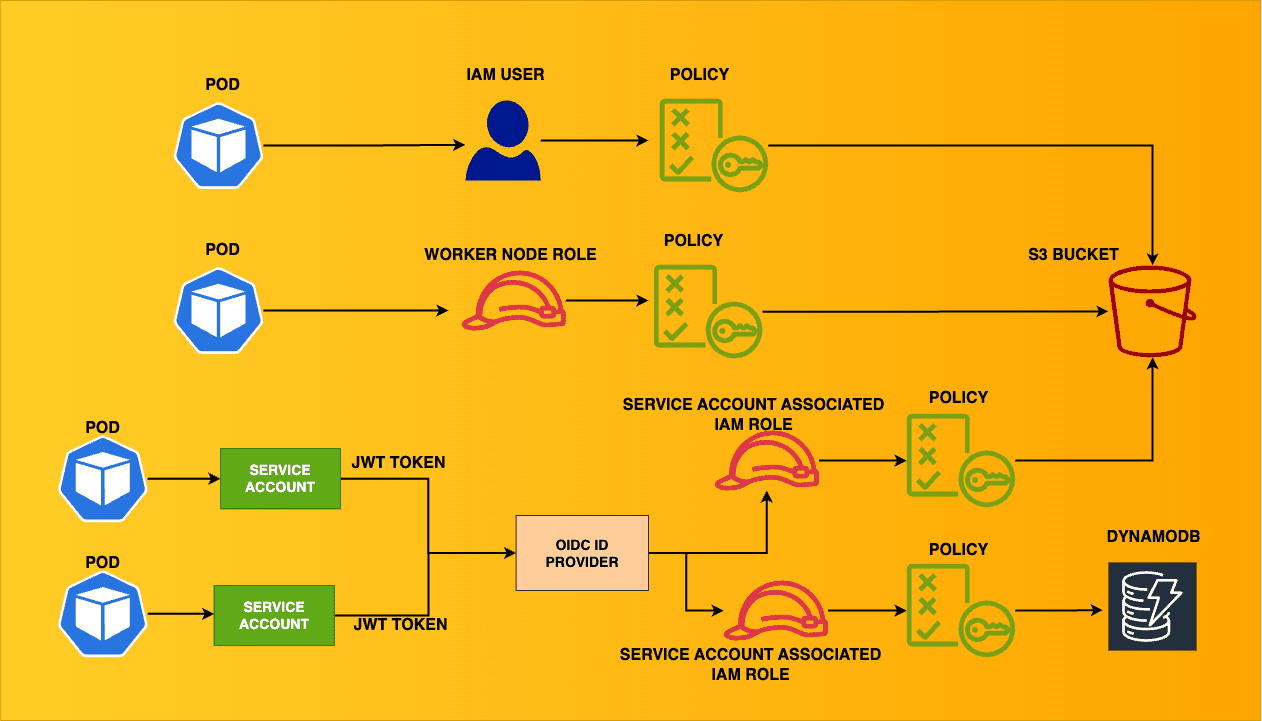
Streamlining IRSA: New Feature EKS Pod Identity Allows Seamless Authentication
A place where imagination meets innovation for everyone (no coding required)
Learn EKS security with EKS Cluster Games
Ensuring least-privilege access in Kubernetes can be complex at times for security & DevOps teams. This blog aims to cover a variety of scenarios where the EKS cluster connects with other AWS resources. This is the architecture of the multiple scenar...
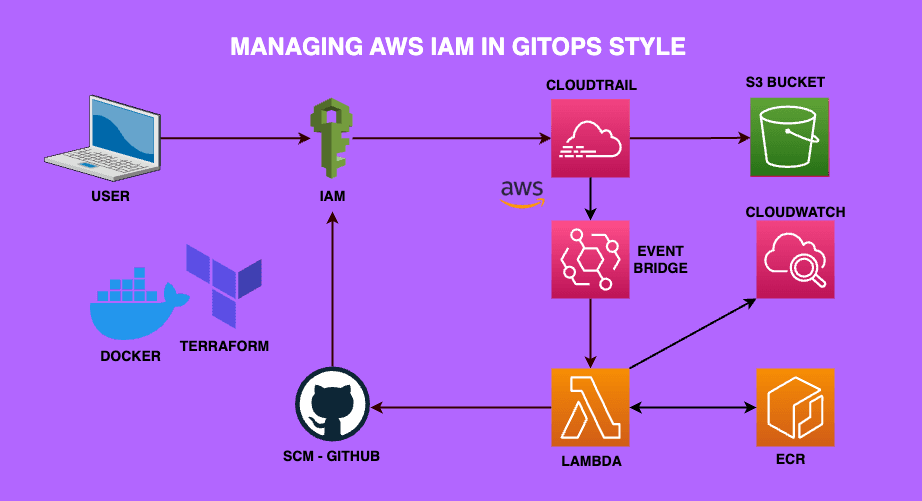
Are you new to AWS & looking for a project to get your hands dirty? This beginner-friendly AWS project focuses on managing AWS IAM using GitOps